IIS/ASP.NET will not serve direct requests to Web.config, which protects possibly sensitive information (e.g. connection strings, email addresses) from the public...at least in theory.
You can further protect web.config information via encryption. Out of the box, the aspnet_regiis.exe utility will encrypt web.config according to your preferences.
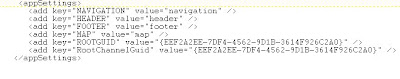
Here is a sample <appsettings> section:
Assume that this application runs under http://localhost/myApp, we could run the following command to encrypt:
- aspnet_regiis -pe "appSettings" -app "/myApp"
Implementing Code to Retrieve Configuration Settings
What's great is that the code that accesses the configuration settings need not change, e.g.:
- string strGUID = ConfigurationSettings.AppSettings["ROOTGUID"];
...would work before and after encryption.
Decryption
To decrypt the configuration settings, just substitute a "-pd" switch for "-pe":
- aspnet_regiis -pd "appSettings" -app "/myApp"
...Finally, I came across a good article about handling this encryption/decryption programmatically (e.g. via an ASP.NET page or a Console App). Here's the 4gfr link.



15 comments:
two questions ??
1: What version of Dot NEt is this for ?
2: If you can decrypt with that command - then so can anyone who gets the file..am I correct ?
1: 2.0 and forward
2: No, you need the crypto container residing in your computer as well
Great site!!! this information really helped me
What's up friends, pleasant post and good urging commented here, I am really enjoying by these.
my homepage; visit website
If you desire to grow your experience simply keep visiting this web site and be updated with the hottest information posted here.
Stop by my weblog: How Webcams May Assist Folks Communicate
An outstanding share! I have just forwarded
this onto a friend who has been conducting
a little homework on this. And he in fact ordered me breakfast because I stumbled upon it for him.
.. lol. So allow me to reword this.... Thanks for the meal!
! But yeah, thanks for spending some time to discuss this issue here on your blog.
My web-site ... Email Console
Hello, I wish for to subscribe for this web site to take newest updates, therefore where can i do it please
help.
Review my website - Email Console
I do not even know how I ended up here, but I thought this post
was great. I do not know who you are but certainly you're going to a famous blogger if you aren't already ;) Cheers!
Stop by my website :: http://pornharvest.com/index.php?m=2501256
Awesome! Its in fact remarkable piece of writing, I have
got much clear idea regarding from this piece of writing.
My web site: hot kamilla stripping
Hello to every one, the contents present at this site are truly remarkable
for people experience, well, keep up the nice work fellows.
Also visit my website - http://photo.hiyong.com/xe/index.php?mid=baby&comment_srl=209&Sort_index=Readed_count&Order_type=asc&page=8&listStyle=webzine&document_srl=8982
This is really fascinating, You're a very professional blogger. I have joined your rss feed and stay up for in search of extra of your excellent post. Additionally, I have shared your website in my social networks
Also visit my web page http://pornharvest.com/index.php?m=2216152
Sweet blog! I found it while searching on Yahoo News.
Do you have any tips on how to get listed in Yahoo News?
I've been trying for a while but I never seem to get there! Many thanks
My blog; Discover More Here
Hi! I could have sworn I've visited this web site before but after looking at some of the articles I realized it's new to
me. Anyways, I'm certainly happy I discovered it and I'll be bookmarking it and checking back regularly!
Visit my web-site :: her explanation
Magnificent web site. A lot of helpful information here.
I'm sending it to a few buddies ans additionally sharing in delicious. And certainly, thank you to your sweat!
My web site: http://pornharvest.com/index.php?m=2208041
Good day! I know this is kind of off topic but I was wondering which blog platform are you using
for this website? I'm getting fed up of Wordpress because I've had problems with hackers and I'm looking at alternatives for another platform. I would be great if you could point me in the direction of a good platform.
Have a look at my web-site; naughty teen brunette gets fucked by a senior on a camping
Post a Comment